On Jan. 15, Minister for Communications and Information S Iswaran stated in Parliament that the identity of the attacker behind the Singhealth cyber attack is known although it will not be revealed for national security reasons.
What is known however, is that the work of the attacker bore the characteristics of an Advanced Persistent Threat (APT) group, according to the Jan. 10 release of the report by the Committee of Inquiry (COI) looking into the cyber attack on SingHealth’s medical data.
According to Iswaran, APT:
"...is a class of cyber-attackers, typically state-linked, who conduct extended cyber campaigns to steal information or disrupt operations."
Additionally, the COI found that:
"...the attacker was well-resourced, and had used advanced techniques and tools to target the SingHealth patient database and illegally exfiltrate patient data. The attacker was persistent, evaded detection for a long time, and even re-entered the network after being detected."
Iswaran said that "appropriate action" has since been taken.
Attack will not stop Smart Nation
Iswaran added however, that such an attack will not derail the Smart Nation initiatives that can enhance economic competitiveness and deliver better public services in Singapore.
The COI report also gave 16 recommendations to strengthen Singhealth's patient database system and public sector IT systems which contain large databases of personal data.
Iswaran added that the Government accepted all of the COI's recommendations and would adopt them to improve cybersecurity, so as to better enable Smart Nation ambitions.
What are the recommendations?
Iswaran summarised the 16 recommendations in his statement by classifying them into four categories: People, Process, Technology and Partnerships.
On People, Iswaran said given that the COI had found that front-end users were the weakest link in a cyberattack, and that it was also such people who first notice an incident is underway, the recommendations by the COI included:
"enhancing cyber hygiene practices, building a culture of cybersecurity across the entire organisation, and ensuring that IT staff are well-trained and equipped to respond to cybersecurity incidents."
For the category of Processes, Iswaran said that the recommendations called for clear plans and standard operating procedures (SOP), along with regular scenario exercises to test such measures. Additionally:
"There also should be regular and comprehensive checks to identify vulnerabilities and high-risk areas, accompanied by audit and compliance checks to ensure that the identified gaps have been plugged.
As for Technology, the COI proposed several measures in strengthening cybersecurity for better prevention and responses to future attacks. Such measures included:
"stronger encryption for data; heightened monitoring of database activity; and an integrated system to aggregate and analyse threat information in real-time, and rapidly isolate and contain the infected system."
Finally, for Partnerships, Iswaran pointed out that the COI had called for improve collective security given Singapore's high connectivity and high value as a target. This would involve better coordination between the the Government, industry and international partners, in areas such as threat intelligence sharing.
Related stories:
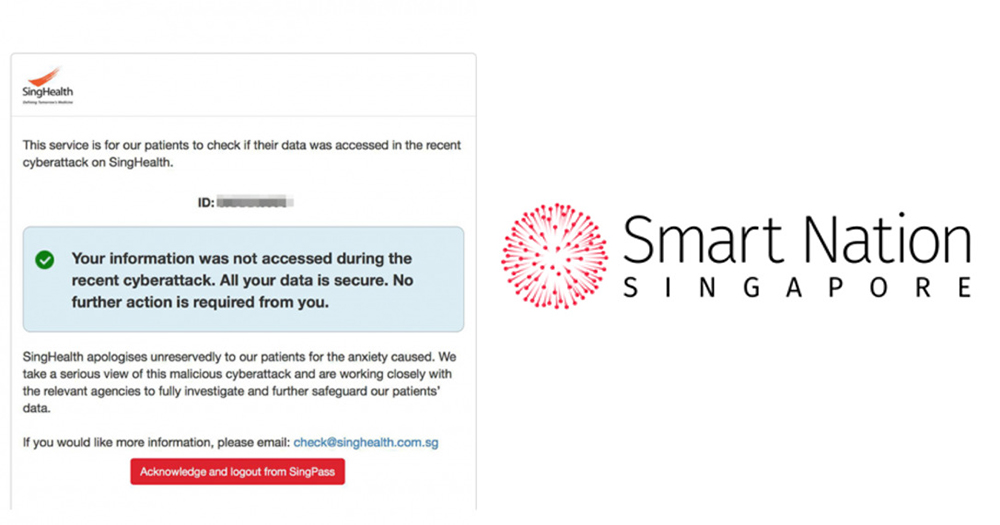
Top image collage from Singhealth Screenshot and Smart Nation Singapore Facebook
If you like what you read, follow us on Facebook, Instagram, Twitter and Telegram to get the latest updates.